Cybernous.com offers expert-led CISSP Training online, empowering professionals to master cybersecurity management, risk, and governance skills. Prepare for industry-leading certifications with practical, up-to-date training and boost your cybersecurity career globally.
-
90 Posts
-
40 Photos
-
2 Videos
-
Cybernous Infosec Consulting at https://www.cybernous.com/
-
Lives in #167, 6th Main, Vinayaka Nagar, Yelahanka
-
Female
-
Followed by 141 people
Recent Updates
-
With increasing cyber attacks, companies are actively looking for skilled professionals who can protect systems and data. That’s where the Offensive Security Specialist: Zero to Hero course by Cybernous comes in. It is designed especially for beginners who want to build a career in ethical hacking and offensive security from scratch.
Read: https://cybernousinfosecconsulting.blogspot.com/2026/04/offensive-security-specialist-zero-to.htmlWith increasing cyber attacks, companies are actively looking for skilled professionals who can protect systems and data. That’s where the Offensive Security Specialist: Zero to Hero course by Cybernous comes in. It is designed especially for beginners who want to build a career in ethical hacking and offensive security from scratch. Read: https://cybernousinfosecconsulting.blogspot.com/2026/04/offensive-security-specialist-zero-to.html0 Comments 0 Shares 0 Views 0 ReviewsPlease log in to like, share and comment! -
Biggest Mistake Self-Taught Hackers Make
Most beginners jump straight into tools like Nmap, Burp, and Metasploit… but forget one thing — methodology.
Without a clear process, skills stay scattered and growth slows down.
👉 Focus on the right approach:
• Recon & Scoping
• Enumeration & Scanning
• Exploitation & Escalation
• Reporting & Remediation
Tools don’t make you a hacker — your process does.
💡 Learn smart. Practice with purpose. Grow faster. Visit: https://www.cybernous.com/
#[11240] #[27797] #[97202] #[31314] #[110916] #[110917] #[20208]Biggest Mistake Self-Taught Hackers Make Most beginners jump straight into tools like Nmap, Burp, and Metasploit… but forget one thing — methodology. Without a clear process, skills stay scattered and growth slows down. 👉 Focus on the right approach: • Recon & Scoping • Enumeration & Scanning • Exploitation & Escalation • Reporting & Remediation Tools don’t make you a hacker — your process does. 💡 Learn smart. Practice with purpose. Grow faster. Visit: https://www.cybernous.com/ #[11240] #[27797] #[97202] #[31314] #[110916] #[110917] #[20208]0 Comments 0 Shares 0 Views 0 Reviews -
3 Cybersecurity Roles Paying ₹20L+ in India
Offensive security is booming—and high-paying roles are open right now. From Penetration Testing Leads to Cloud Security Engineers and Security Architects, companies across BFSI, SaaS, and fintech are hiring skilled professionals.
Our 70-hour hands-on program helps you go from beginner to pentest-ready with real labs and a CTF project.
Batch starts 27 April 2026. Limited seats—start building your cybersecurity career today.
📞 Call/WhatsApp: +91 8595338705
📧 contact@[39336].com
🌐 www.cybernous.com
🔗 View Course Details & Enroll → https://lnkd.in/gWyadE-y3 Cybersecurity Roles Paying ₹20L+ in India Offensive security is booming—and high-paying roles are open right now. From Penetration Testing Leads to Cloud Security Engineers and Security Architects, companies across BFSI, SaaS, and fintech are hiring skilled professionals. Our 70-hour hands-on program helps you go from beginner to pentest-ready with real labs and a CTF project. Batch starts 27 April 2026. Limited seats—start building your cybersecurity career today. 📞 Call/WhatsApp: +91 8595338705 📧 contact@[39336].com 🌐 www.cybernous.com 🔗 View Course Details & Enroll → https://lnkd.in/gWyadE-y0 Comments 0 Shares 0 Views 0 Reviews -
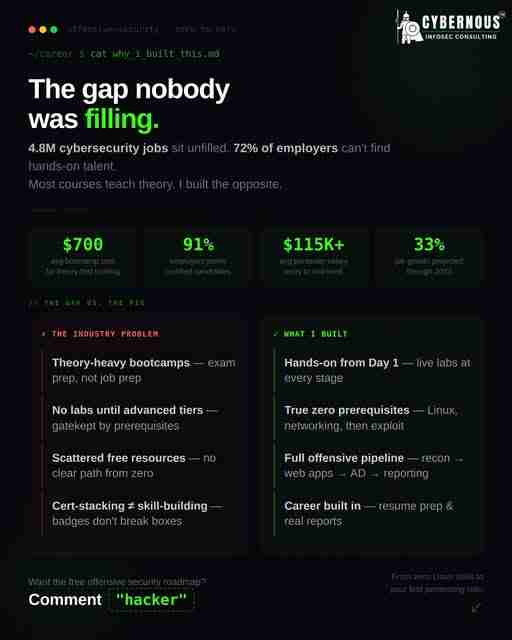
4.8M cybersecurity jobs are unfilled, and most courses still teach theory over real skills. I built a 100% hands-on program where you start hacking from day one—no prerequisites, just practical labs, real workflows, and a capstone CTF. In 70 hours, you go from beginner to pentest-ready. Batch starts April 27. Limited seats—don’t miss out. Comment “hacker” for a free roadmap or enroll now. Build confidence, reports, and launch cybersecurity career.
⚡ Limited seats. Don't wait for the next one. Ready to start your offensive security career? 📞 Call/WhatsApp: +91 8595338705 📧 contact@[39336].com 🌐 www.cybernous.com 🔗 View Course Details & Enroll → https://lnkd.in/gWyadE-y
#[11240] #[27797] #[97202] #[31314] #[34675]4.8M cybersecurity jobs are unfilled, and most courses still teach theory over real skills. I built a 100% hands-on program where you start hacking from day one—no prerequisites, just practical labs, real workflows, and a capstone CTF. In 70 hours, you go from beginner to pentest-ready. Batch starts April 27. Limited seats—don’t miss out. Comment “hacker” for a free roadmap or enroll now. Build confidence, reports, and launch cybersecurity career. ⚡ Limited seats. Don't wait for the next one. Ready to start your offensive security career? 📞 Call/WhatsApp: +91 8595338705 📧 contact@[39336].com 🌐 www.cybernous.com 🔗 View Course Details & Enroll → https://lnkd.in/gWyadE-y #[11240] #[27797] #[97202] #[31314] #[34675]0 Comments 0 Shares 0 Views 0 Reviews -
In today’s rapidly evolving cybersecurity landscape, professionals aiming to step into leadership roles often pursue the CISM certification. Unlike purely technical certifications, CISM focuses on governance, risk management, and aligning security strategies with business objectives. This makes preparation more challenging, as success requires both conceptual clarity and a managerial mindset.
Read: https://cybernousinfosecconsulting.blogspot.com/2026/04/mastering-cism-structured-path-to.htmlIn today’s rapidly evolving cybersecurity landscape, professionals aiming to step into leadership roles often pursue the CISM certification. Unlike purely technical certifications, CISM focuses on governance, risk management, and aligning security strategies with business objectives. This makes preparation more challenging, as success requires both conceptual clarity and a managerial mindset. Read: https://cybernousinfosecconsulting.blogspot.com/2026/04/mastering-cism-structured-path-to.html0 Comments 0 Shares 0 Views 0 Reviews -
🚨 Registrations OPEN — April 2026 Batch! 🚨
Start your cybersecurity journey and become an Offensive Security Specialist 🚀
✔ 70 hours live training
✔ Hands-on labs + CTF
✔ Learn pentesting, OWASP, networking & reporting
No experience needed—just the right guidance.
📅 Starts: 27 April 2026
📞 +91 8595338705
🌐 www.cybernous.com
#[11240] #[27797] #[30432] #[57203] #[28505] #[31314] #[52474]🚨 Registrations OPEN — April 2026 Batch! 🚨 Start your cybersecurity journey and become an Offensive Security Specialist 🚀 ✔ 70 hours live training ✔ Hands-on labs + CTF ✔ Learn pentesting, OWASP, networking & reporting No experience needed—just the right guidance. 📅 Starts: 27 April 2026 📞 +91 8595338705 🌐 www.cybernous.com #[11240] #[27797] #[30432] #[57203] #[28505] #[31314] #[52474]0 Comments 0 Shares 0 Views 0 Reviews -
In today’s digital world, businesses depend heavily on technology. From storing data to running operations, everything is connected to IT systems. But with this dependence comes risk—data breaches, system failures, and security threats. That’s where a Certified Information Systems Auditor (CISA) becomes important.
read: https://cybernouscom.wordpress.com/2026/04/06/certified-information-systems-auditor-a-simple-guide-to-cisa-certification/In today’s digital world, businesses depend heavily on technology. From storing data to running operations, everything is connected to IT systems. But with this dependence comes risk—data breaches, system failures, and security threats. That’s where a Certified Information Systems Auditor (CISA) becomes important. read: https://cybernouscom.wordpress.com/2026/04/06/certified-information-systems-auditor-a-simple-guide-to-cisa-certification/0 Comments 0 Shares 0 Views 0 Reviews -
This is where CISSP Online Training plays a crucial role. Recognized globally, the CISSP (Certified Information Systems Security Professional) certification is a benchmark for experienced security professionals aiming to advance their careers.
Read: https://medium.com/@cybernous/cissp-online-training-build-global-cybersecurity-leadership-skills-bf2765c8c06dThis is where CISSP Online Training plays a crucial role. Recognized globally, the CISSP (Certified Information Systems Security Professional) certification is a benchmark for experienced security professionals aiming to advance their careers. Read: https://medium.com/@cybernous/cissp-online-training-build-global-cybersecurity-leadership-skills-bf2765c8c06d0 Comments 0 Shares 0 Views 0 Reviews -
As recent industry reports show, a large portion of cyber incidents stem from vulnerabilities in third-party ecosystems. This makes Third-Party Risk Management (TPRM) one of the most critical disciplines for modern enterprises to master.
https://medium.com/@cybernous/tprm-online-training-bootcamp-master-third-party-risk-management-with-confidence-d6c9d58c62f0As recent industry reports show, a large portion of cyber incidents stem from vulnerabilities in third-party ecosystems. This makes Third-Party Risk Management (TPRM) one of the most critical disciplines for modern enterprises to master. https://medium.com/@cybernous/tprm-online-training-bootcamp-master-third-party-risk-management-with-confidence-d6c9d58c62f00 Comments 0 Shares 0 Views 0 Reviews -
Organizations across industries face constant risks from malware, ransomware, phishing attacks, and advanced persistent threats. At the center of this battle stands the Security Operations Center (SOC) Analyst — the professional responsible for monitoring, detecting, and responding to security incidents in real time.
Read: https://medium.com/@cybernous/soc-analyst-building-the-front-line-of-cyber-defense-28022c72d7edOrganizations across industries face constant risks from malware, ransomware, phishing attacks, and advanced persistent threats. At the center of this battle stands the Security Operations Center (SOC) Analyst — the professional responsible for monitoring, detecting, and responding to security incidents in real time. Read: https://medium.com/@cybernous/soc-analyst-building-the-front-line-of-cyber-defense-28022c72d7ed0 Comments 0 Shares 0 Views 0 Reviews -
At the heart of every SOC is a skilled SOC Analyst. SOC Analyst training is designed to prepare aspiring cybersecurity professionals to take on this critical role with confidence and practical expertise.
Read: https://cissp.hashnode.dev/soc-analyst-training-build-a-career-on-the-frontlines-of-cybersecurityAt the heart of every SOC is a skilled SOC Analyst. SOC Analyst training is designed to prepare aspiring cybersecurity professionals to take on this critical role with confidence and practical expertise. Read: https://cissp.hashnode.dev/soc-analyst-training-build-a-career-on-the-frontlines-of-cybersecurity0 Comments 0 Shares 0 Views 0 Reviews -
Organizations across industries are seeking professionals who can design, manage, and govern robust security programs at an enterprise level. This is where CISSP training online becomes a game-changer for experienced security professionals aiming to step into leadership roles.
Read: https://medium.com/@cybernous/cissp-training-online-build-elite-cybersecurity-leadership-skills-57f1adf5dcb4Organizations across industries are seeking professionals who can design, manage, and govern robust security programs at an enterprise level. This is where CISSP training online becomes a game-changer for experienced security professionals aiming to step into leadership roles. Read: https://medium.com/@cybernous/cissp-training-online-build-elite-cybersecurity-leadership-skills-57f1adf5dcb40 Comments 0 Shares 0 Views 0 Reviews
More Stories